Multi-Factor Authentication for the default authentication method – 3900.82
Blackboard Learn SaaS
Ultra Experience
Impact: All users
Related topics: Identification and Authorization, Quick start for Blackboard App
Some institutions enforce Multi-Factor Authentication (MFA) to fulfill security policies and best practices. To better support these institutions, we now offer a second authentication factor for the internal authentication method (where a user provides a username and password).
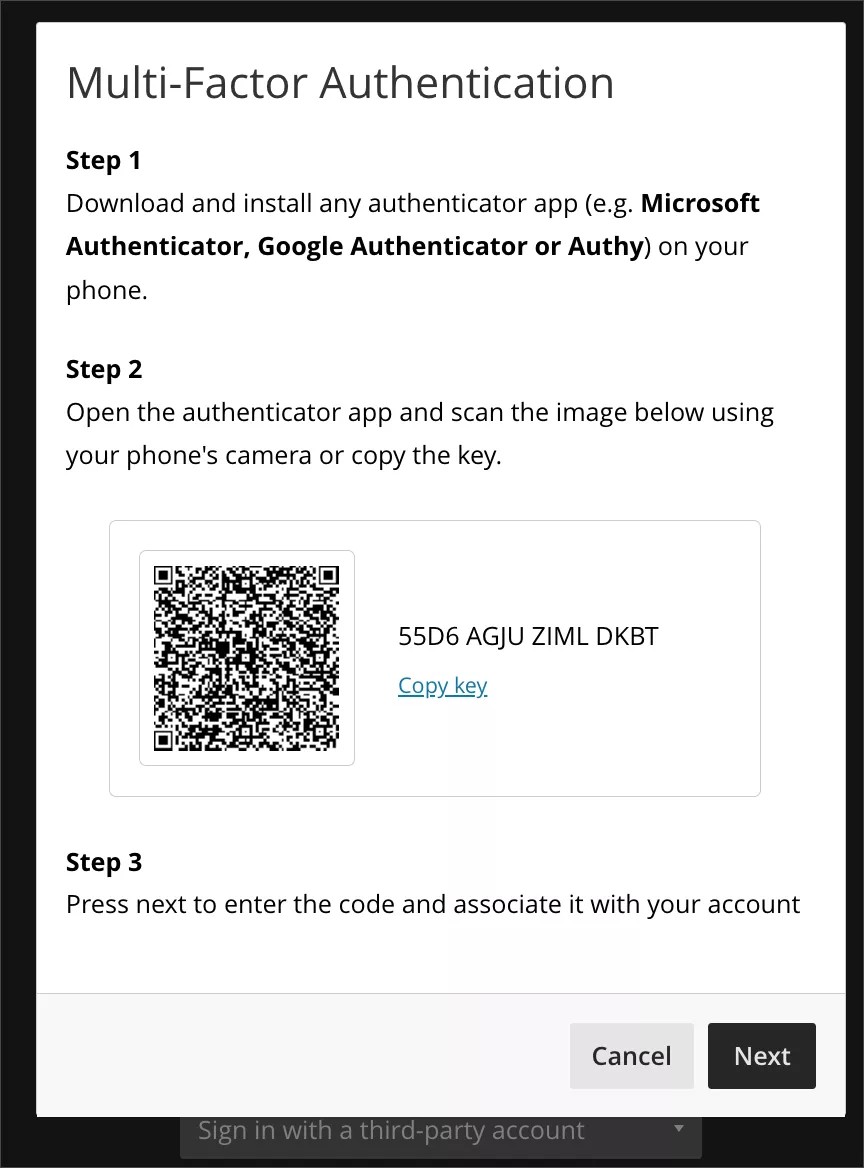
When the administrator enables MFA, users start the MFA registration process after providing a correct username and password. Users can use an authenticator app of their preference or the one suggested by their institution.
Image 1. Initial instructions described in the MFA registration process
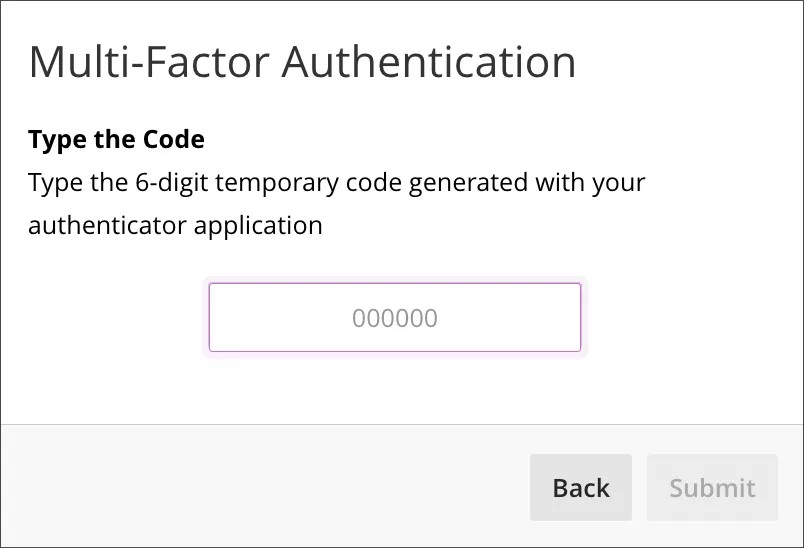
Image 2. Request of temporary code to complete MFA registration
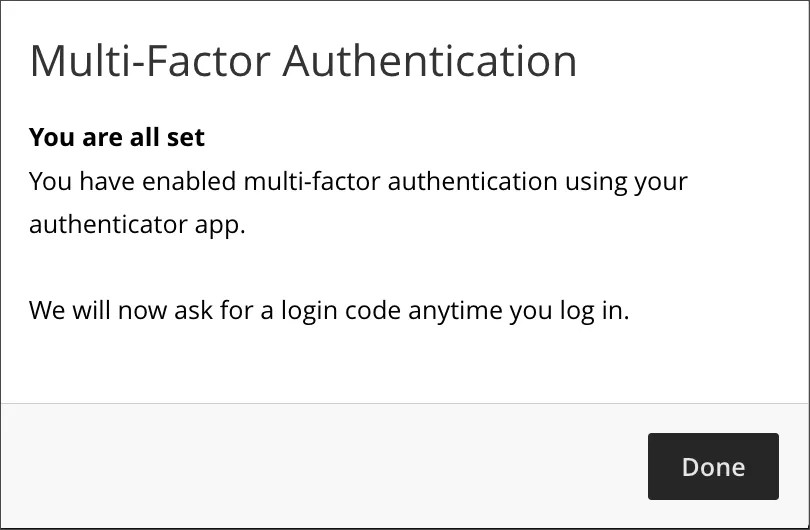
Image 3. Confirmation of successful MFA registration
Users are asked for a code generated by the authentication app on their trusted device(s) each time they log in.
If a user loses access to their trusted device, they can request a reset of their MFA (via normal institution-defined support channels). This allows the user to start the registration process of a new device.
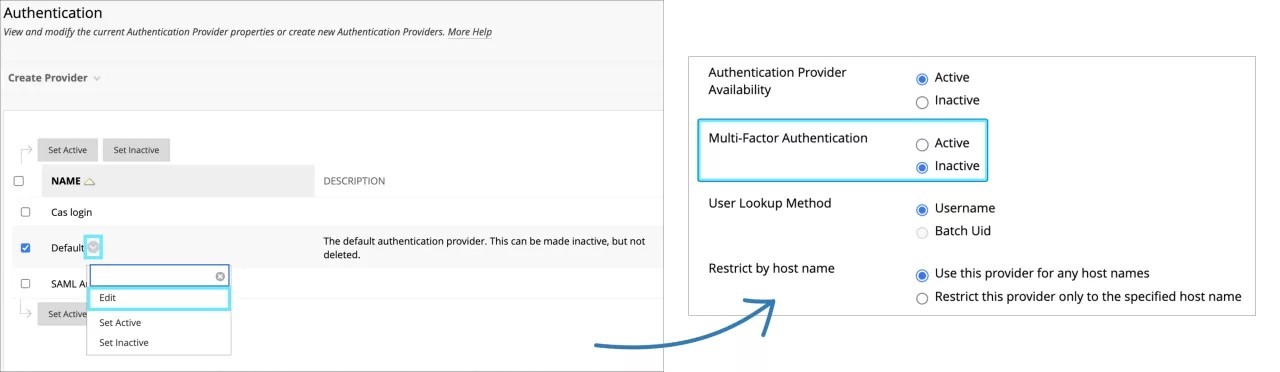
For administrators: MFA is inactive by default. MFA is compatible with any kind of authenticator app.
For this release, MFA is only compatible with the Force to Web authentication method in the mobile App. If the institution has the native authentication method activated, the users won’t be asked to enter the TOTP code when logging in the mobile app. Compatibility with the native authentication method will be available in a future release.
To set MFA to active, go to the Administrator Tool Panel -> Integrations -> Authentication -> Default -> Edit -> Multifactor Authentication -> Active.
Image 4. Enable MFA feature from Administrator Tool Panel
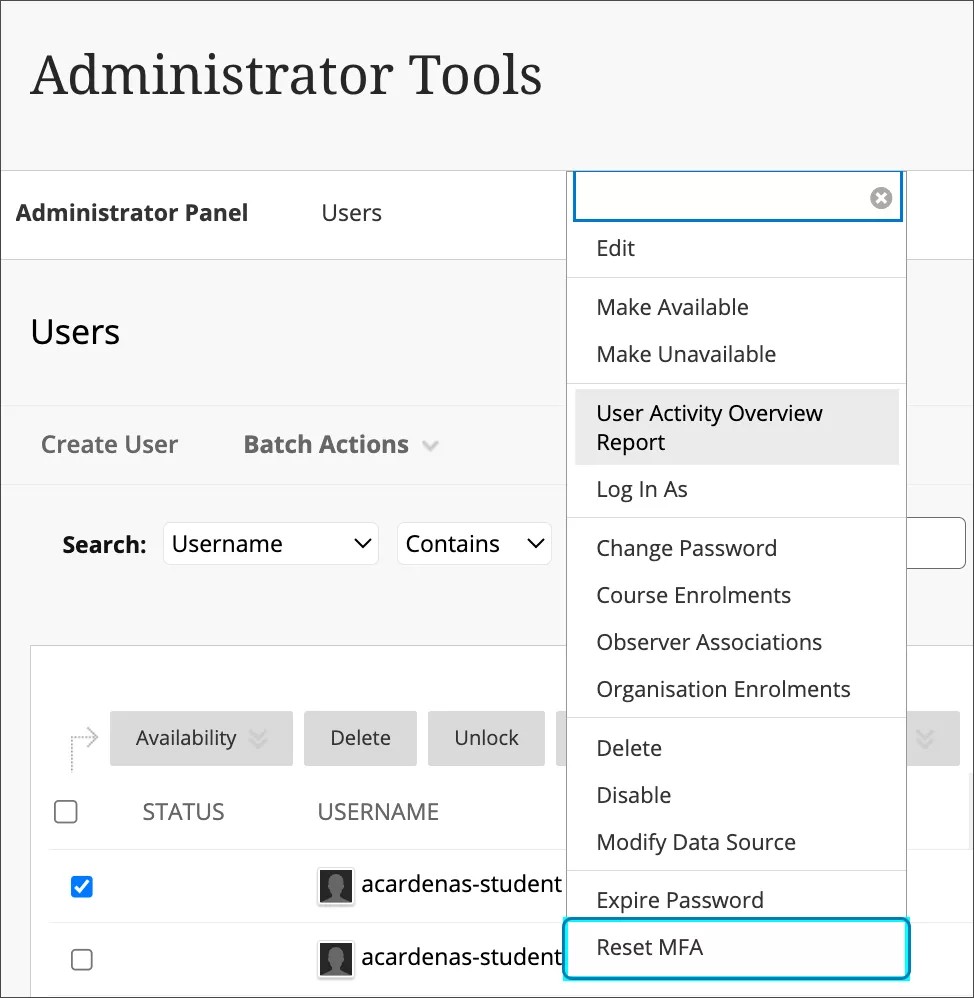
To reset a user’s MFA, go to Administrator Tool Panel -> Users -> Search and select user -> Reset MFA.
Image 5. Reset MFA for a specific user
MFA is compatible with the Account Locking feature. To protect accounts from unauthorized access, we recommend enabling the Account Locking feature. To confirm the current configuration, go to the Administrator Tool Panel -> Account Lock Settings -> Enable Account -> Locking.
For audit and monitoring purposes, events related to MFA log in and reset can be found in Administrator Tool Panel -> Tools and Utilities -> Logs -> Authentication Logs.