Google Chrome and Mozilla Firefox have implemented Mixed Content Blocking processes to protect computers from security attacks exposed via unsecured content referenced from secured pages.
What is mixed content and why does it matter?
Websites that ask for sensitive information, such as usernames and passwords, often use secure (https) connections to transmit content to and from the computer you're using. If you're visiting a site via a secure connection both Google Chrome and Firefox verify that the content on the webpage has been transmitted safely. If either browser detects certain types of content on the page coming from insecure (http) channels, the browser will automatically prevent the content from loading and you'll see a shield icon appear in the address bar.
By blocking the content and possible security gaps, Chrome and Firefox protects your information on the page from falling into the wrong hands.
Mixed content types
Two types of content impact the user experience of viewing a web page and, in the context of Mixed Content, each has various levels of risk:
- Mixed passive content or display content
- Mixed active content or script content
Mixed passive content or display content
Mixed Passive Content is HTTP Content on an HTTPS website that cannot alter the Document Object Model (DOM) of the webpage. More simply stated, Passive HTTP content has a limited effect on the HTTPS website. For example, an attacker could replace an image served over HTTP with an inappropriate image or a misleading message to the user. However, the attacker would not have the ability to affect the rest of the webpage, only the section of the page where the image is loaded.
An attacker may infer information about user browsing activity by observing which images are served to the user, thus deriving pages viewed. Also, by observing HTTP headers sent to retrieve and deliver the image the attacker may view the user agent string and any cookies associated with the domain the image is requested from. If the content is served from the same domain as the main webpage, then session information is potentially exposed circumventing the protection HTTPS provides to the user account.
Examples of Passive Content are images, audio, and video loads.
Mixed active content or script content
Active Content is content that has access to and can affect all or parts of the Document Object Model (DOM) of an HTTPS page. This type of mixed content can alter the behavior of an HTTPS page and potentially steal sensitive data from the user. In addition to the risks already described for Mixed Passive Content above, Mixed Active Content is also exposed to a number of potential attack vectors.
Example: A Man In The Middle (MITM) attacker can intercept requests for HTTP active content. The attacker can then rewrite the response to include malicious JavaScript code. Malicious script can steal the user's credentials, acquire sensitive data about the user, or attempt to install malware on the user's system (by leveraging vulnerable plugins the user has installed, for example).
Examples of Active Content are JavaScript, CSS, objects, xhr requests, iframes, and fonts.
Eliminate the need for user browser controls
To improve user experience and eliminate the need for users to adjust browser settings, all content should be served over HTTPS.
Browser management of mixed content
After reviewing the examples on Mozilla's website, you will see the impact of mixed content on the user browsing experience and understand the impact browser settings have on page rendering.
Note that mixed content blocking concepts are similar across browsers and that the management of access and levels of information are the main differences between browsers supporting mixed content blocking.
Secure web pages served over HTTPS may include insecure elements that can leave your information vulnerable to attacks. When a page contains both secure and insecure elements, it's called Mixed Content.
To protect you from the risks related to Mixed Content, Mozilla Firefox blocks insecure content from appearing on otherwise secure pages. If you feel comfortable navigating a page containing insecure elements, you can choose to view this content in a few steps. This article describes how to manage browser controls for accessing Mixed Content for Mozilla Firefox browsers v23 and later.
Manage blocked content settings
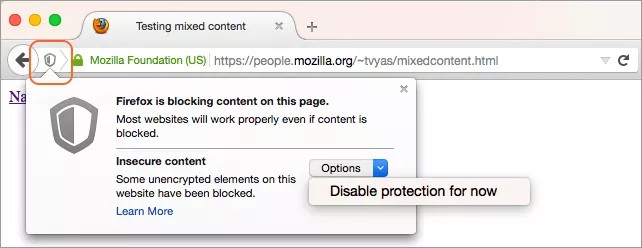
When you visit a page with Mixed Content in Firefox, a shield will appear in the location bar. This indicates that some content has been blocked. Select the icon to temporarily disable this security feature and view the insecure content.
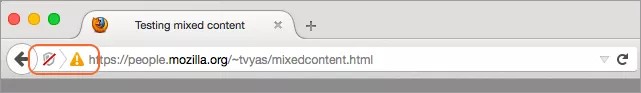
Select Disable protection for now if you want to view this content. The page will reload and two icons will appear in the location bar, a shield with a red line through it and a yellow triangle with an exclamation point. These icons are there to remind you that some content on the page may be putting your information at risk.
Firefox: Mixed Content Blocking
Mozilla Firefox uses Mixed Content Blocking to protect your information, but it also allows you to choose whether or not you want to view Mixed Active Content. This type of content can alter how an entire page behaves and potentially steal a user's sensitive data. Mixed Passive Content, however, does not have the ability to alter the entire page's behavior, but only the piece of HTTP (insecure) content itself.
Mixed Passive Content is common online and includes web page elements such as images, audio, and video. Firefox does not automatically block this type of content because it would break a lot of web pages and diminish user experience. However, there is a way to block mixed passive content by editing your browser's configuration.
Further reading
More information on Mixed Content can be found in the following articles at Mozilla's website:
- How does content that isn't secure affect my safety? Mozilla Support.
- Mixed Content Blocking Enabled in Firefox 23! Tanvi's Blog, Security Engineering at Mozilla.